From Backdoors to “Upload Moderation”: Is Your Privacy Under Attack?
Are We Trading Privacy for Policing?
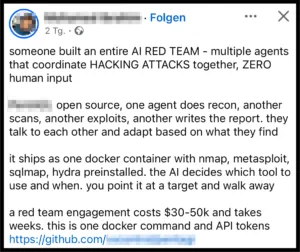
The EU’s “Going Dark” group says it’s about helping law enforcement tackle digital crime. But dig a little deeper, and things get murky. With talk of encryption backdoors, data retention revivals, and pressure on tech companies to play surveillance middlemen, critics warn we’re inching toward mass surveillance. Austria’s already setting the stage with its own plans to monitor messenger apps. Is this really about security, or are we breaking the very tools that protect our privacy? Let’s unpack it.